Question:
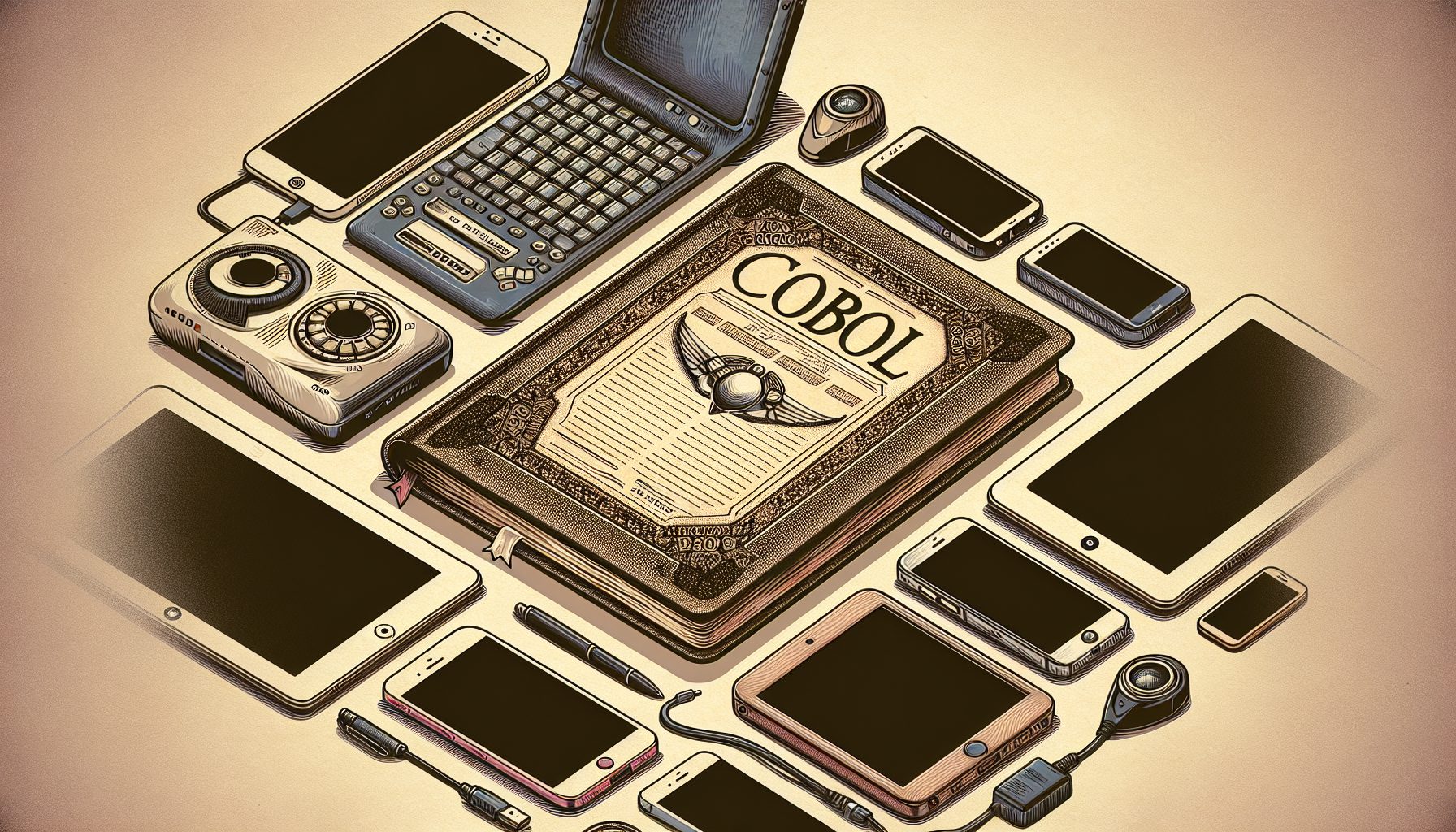
In my program, the user must log in. I must take that login and search a database to see if the login is valid and then match a password with it. A friend told me it would be real easy to make an Access database to do this, but I don’t know how to use Access all that well. Is there an easier way?
Answer:
This is a fairly simple application. Without giving away all the details (as you’re a student), you first create a new Access database. Next, you build a table in it that has two columns: user ID and password. You can then populate the database with a few rows of data for testing.
Your Visual Basic application then has to have a login form. You can look up the user ID and check the password field against what was typed in. If it passes, life goes on. Otherwise, show a message box and return to the form.