You usually do not feel the architecture breaking all at once. You feel it first in the way latency stops being local and starts becoming systemic. A single slow dependency turns into a queue growth. A harmless retry policy turns into a traffic amplifier. P99 climbs while average latency stays polite enough to pass dashboards and status meetings. That is the dangerous phase, because the system still looks functional right up until the next product win, region launch, or customer onboarding wave turns it into an incident factory.
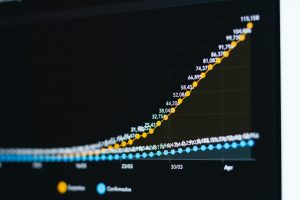
Latency is not just a performance metric. At scale, it is an architectural diagnostic. It exposes coupling, backpressure weaknesses, data access mistakes, and coordination patterns that were survivable at one order of magnitude but will fail at the next. If you want an early warning system for the next scale jump, watch these seven signals closely. They show that your design still depends on hope more than control.
1. Your p99 moves before your average does
When your architecture starts approaching a scaling boundary, tail latency usually degrades first. Mean latency can stay flat while the 95th and 99th percentiles drift upward under bursty load, uneven shard distribution, or dependency contention. That matters because users do not experience averages. They experience the slowest path through your request graph, especially in fan-out systems where one page load or API call depends on ten or twenty downstream calls.
This is where many teams misread the room. They see a stable average and assume they still have headroom, but the tails are already telling them that coordination cost is rising. In distributed systems, the probability of one slow component affecting the whole request grows with every additional hop. Amazon’s internal focus on tail latency in large-scale services made this point famous for good reason: a system can look statistically healthy while becoming operationally fragile. If p99 is rising faster than throughput, your architecture is already paying a tax for complexity you have not contained.
2. Small traffic spikes create disproportionate latency jumps
A healthy architecture bends under load before it breaks. An unhealthy one falls off a cliff. If a 15 percent traffic increase causes latency to double, you are not looking at a capacity problem alone. You are usually looking at non-linear behavior from shared resources, lock contention, synchronous fan-out, overloaded caches, or queues with no real backpressure strategy.
This is often the moment when teams learn they built for steady-state throughput, not real production variability. Spiky load is normal. Deployments, retries, cache invalidations, batch jobs, noisy neighbors, and customer behavior all create bursts. Google’s SRE work on overload and cascading failure patterns exists because many systems do not fail from sustained peak load. They fail from short-lived amplification events. If the latency response to traffic is non-linear, the next scale jump will not simply cost you more infrastructure. It will expose architectural assumptions that only worked when the system stayed calm.
3. Retries improve the success rate but make incidents worse
Retries are one of the most dangerous ways to hide structural problems. Done carefully, they improve resilience against transient faults. Done casually, they turn latency trouble into dependency collapse. If a service times out, clients retry, queues deepen, thread pools saturate, and the failing dependency receives even more work precisely when it can least handle it. You see a brief success-rate recovery followed by a much uglier incident.
That pattern reveals an architecture that lacks clear budgets for time, concurrency, and failure isolation. A retry is not free work. It is extra load, extra waiting, and extra coordination. Stripe and many high-scale platform teams have written openly about idempotency, timeout budgets, and bounded retries because the naive version causes self-inflicted outages. If your latency profile improves only when you disable retries or aggressively shed load, your architecture is telling you that resilience was bolted on at the edge instead of designed through the full request path.
4. Cache misses behave like mini-outages
Every mature system has cache misses. The warning sign is when cache misses stop looking like a performance event and start looking like a reliability event. If miss storms cause origin latency explosions, database saturation, or lock contention around recomputation, you do not have a cache problem. You have an architectural dependency on cached state for basic survivability.
That distinction matters at scale. A cache should absorb load and improve responsiveness, but the underlying system still has to degrade gracefully when the cache is cold, invalidated, or partitioned. Many teams discover this during a regional failover, a deploy that changes key cardinality, or an expiration policy mistake. Netflix’s broader approach to resilience engineering is relevant here because resilient systems assume supporting layers will fail at inconvenient times. When cache misses produce thundering herds, the next scale jump will widen the blast radius. The architecture has coupled availability to hit rate in a way that will not survive growth.
5. Cross-service calls grow faster than business transactions
One of the clearest latency signals of architectural drift is when the number of internal service calls per external user action keeps rising. A checkout becomes twelve synchronous calls. A dashboard render becomes thirty. A write operation triggers validation, enrichment, entitlement checks, recommendation lookups, audit logging, and half a dozen side effects that all sit on the critical path. The system still works, but each new feature quietly buys more latency and less fault tolerance.
This is the hidden tax of service decomposition without boundary discipline. Microservices are not the problem by themselves. Unchecked request choreography is. The next scale jump hurts because every extra hop multiplies queueing, timeout coordination, and partial failure risk. I have seen teams reduce p99 more by removing three unnecessary synchronous calls than by tuning JVM flags for weeks. That is why Uber’s engineering discussions around service mesh, RPC control, and dependency visibility resonated with so many architects. When business transactions fan out faster than the business itself is growing, your latency is exposing an organization and architecture that no longer agree on what belongs in the hot path.
6. Background work keeps leaking into the request path
Architectures approaching a scaling wall often show a blurry boundary between interactive and asynchronous work. A user request waits for search indexing, analytics emission, permission recomputation, PDF generation, third-party enrichment, or write-after-read consistency work that should have been detached from the immediate response. Latency grows because the critical path has become a dumping ground for anything a team was afraid to make eventual.
There are contexts where stronger consistency or synchronous confirmation is the right call. Payments, inventory control, and security-sensitive flows often justify it. But many systems carry synchronous baggage simply because nobody trusted the asynchronous design enough to commit to it. That is a scaling smell. The next traffic jump will magnify the cost of every non-essential millisecond in the hot path. LinkedIn’s Kafka-centered event architectures helped popularize a more disciplined separation between user-facing latency and downstream processing for exactly this reason. If your request path is still doing work that could safely happen after the response, your architecture is spending latency to compensate for unclear system contracts.
7. Incident mitigation depends on manual traffic shaping
The final signal is operational, but it is deeply architectural. If your playbook for latency incidents relies on engineers manually draining queues, turning off features, rate-limiting specific tenants, flushing caches in the right order, or scaling a fragile dependency before saturation hits, the system is telling you it lacks automatic control loops. Manual heroics do not scale with traffic, service count, or organizational complexity.
Teams sometimes normalize this because experienced operators can keep the platform alive. That works until the next order of magnitude removes the time margin humans were exploiting. Real scalability needs architecture-level governors: admission control, concurrency limits, adaptive shedding, circuit breaking, and isolation boundaries that make bad conditions smaller instead of faster. The lessons from large Kubernetes-based platform teams are consistent here: once cluster, service, and dependency counts grow, control-plane thinking matters as much as raw compute. If latency recovery depends on who is on call and how quickly they recognize the pattern, your architecture will not survive the next scale jump without painful intervention.
Latency is rarely the first thing that breaks, but it is often the first thing that tells the truth. When tail latency rises, spikes become cliffs, retries amplify failure, and caches or operators become structural crutches, the system is revealing where scale will turn inconvenience into outage. The fix is not always more hardware or more tuning. Often, it is fewer synchronous dependencies, better backpressure, clearer service boundaries, and stronger failure isolation. The next scale jump rewards architectures that control work, not just process it.
Senior Software Engineer with a passion for building practical, user-centric applications. He specializes in full-stack development with a strong focus on crafting elegant, performant interfaces and scalable backend solutions. With experience leading teams and delivering robust, end-to-end products, he thrives on solving complex problems through clean and efficient code.