You have probably lived this moment. Traffic is calm, dashboards look healthy, then a campaign launches, a feature hits the front page, or a customer’s cron job goes rogue. QPS spikes 10x in minutes. Latency climbs. Someone asks the inevitable question: “Why didn’t we size for this?”
Designing systems for burst traffic is not about guessing the biggest possible peak and buying your way out. That path leads to chronic overprovisioning, wasted spend, and brittle architectures that still fail in unexpected ways. The real challenge is building systems that stretch under pressure, then snap back to efficiency when the burst passes.
At its core, burst traffic design is about time. How fast demand rises, how long it stays high, and how quickly your system can respond. If you can absorb short spikes cheaply and scale only when demand is sustained, you avoid paying for capacity you rarely use. This article walks through how experienced teams actually do that, drawing from production patterns used at scale, the tradeoffs behind them, and the places where theory breaks down in practice.
What Experts Actually Say About Burst Traffic
We spent time reviewing postmortems, conference talks, and practitioner writeups from teams that regularly deal with unpredictable demand.
Cindy Sridharan, former Principal Engineer at Uber, has repeatedly emphasized that most outages during traffic spikes are not caused by raw load, but by slow failure propagation. Systems that lack backpressure and isolation tend to amplify small spikes into cascading failures.
Adrian Cockcroft, former VP of Cloud Architecture at Netflix, has argued that elastic infrastructure alone is insufficient. In his experience, resilience comes from designing services to degrade gracefully, shedding nonessential work when demand exceeds capacity instead of trying to serve everything.
Charity Majors, CTO at Honeycomb, has pointed out that burst traffic often exposes unknown unknowns. Teams think in averages, but production breaks at the edges. High-cardinality observability and fast feedback loops matter more than perfect capacity models.
Taken together, these perspectives point to a shared conclusion. You do not survive bursts by provisioning for the worst case. You survive by controlling how load enters your system, how it flows through dependencies, and how much work you are willing to drop.
Why Overprovisioning Fails as a Strategy
Overprovisioning feels safe because it is simple. Add more instances, bigger databases, and higher limits. The problem is that bursts are rarely uniform.
A 10x spike at the edge might translate into a 50x spike on a hot shard, a single cache key, or a downstream dependency with stricter limits. Overprovisioning the front door does nothing for those internal choke points.
There is also a financial asymmetry. You pay for idle capacity 24/7, but you only need it during rare events. In cloud environments, this compounds quickly. Teams often discover they are spending more to stay idle than to handle real traffic.
Most importantly, overprovisioning encourages complacency. It delays hard conversations about failure modes, load shedding, and user experience under stress. When the truly unexpected burst arrives, the system still breaks, just at a larger scale.
Design Principle 1: Decouple Traffic Spikes from Work
The first lever you should reach for is decoupling. Not every request needs to be processed immediately.
Queues, streams, and buffers turn bursty traffic into a smoother flow of work. When a spike hits, you accept requests quickly, enqueue them, and process them at a rate your system can sustain.
This pattern shows up everywhere for a reason. Message queues absorb bursts cheaply, often orders of magnitude cheaper than keeping compute hot. They also give you explicit control over backpressure.
The key design decision is deciding what can be delayed. User-facing reads often need low latency. Writes, analytics events, notifications, and background processing usually do not.
A simple worked example makes this concrete. Suppose your steady-state system can process 5,000 jobs per second. A burst sends 100,000 jobs over 10 seconds, or 10,000 per second. Without a buffer, you need to double the capacity instantly. With a queue, you absorb the extra 50,000 jobs and drain them over the next 10 seconds at steady capacity. The user sees slightly delayed processing, but the system stays stable.
Design Principle 2: Scale on Signal, Not on Panic
Autoscaling is often treated as the answer to burst traffic, but naive autoscaling frequently makes things worse.
If you scale on instantaneous metrics like CPU spikes, you chase noise. Cold starts add latency. New instances arrive after the worst of the burst has passed, leaving you overprovisioned again.
Experienced teams scale on sustained signals. They look for trends over tens of seconds or minutes, not milliseconds. They combine multiple signals, queue depth plus request latency, error rates, plus saturation indicators.
This is where predictive scaling earns its keep. If you know that traffic spikes every weekday at 9 am, or during product launches, you pre-warm capacity just in time, then scale it back down. You pay for minutes, not hours.
The uncomfortable truth is that autoscaling is a control system. Poorly tuned control systems oscillate. Well-tuned ones respond smoothly. Most outages blamed on “traffic spikes” are actually control failures.
Design Principle 3: Fail Cheaply and Intentionally
When the load exceeds capacity, something must give. You get to choose what.
Graceful degradation means deciding in advance which features are optional. Maybe recommendations disappear. Maybe search results are cached longer. Maybe write-heavy endpoints return “accepted” instead of blocking.
Rate limiting is the simplest form of intentional failure. It protects your core systems by rejecting excess load early, when it is cheapest to do so. Importantly, rate limits should be dynamic and tiered. Protect internal services more aggressively than external APIs. Protect write paths more than reads.
Circuit breakers serve a similar role for dependencies. If a downstream service is slow or failing, stop sending traffic. Let it recover instead of dragging the whole system down.
These techniques feel harsh, but users prefer partial functionality over total outages. From a business perspective, serving 80 percent of requests reliably beats failing 100 percent spectacularly.
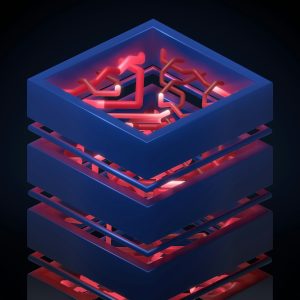
A Practical Architecture Pattern for Bursty Systems
Here is a pattern that shows up again and again in real systems:
-
A thin edge layer that authenticates, rate-limits, and quickly acknowledges requests.
-
Asynchronous ingestion into queues or streams for bursty workloads.
-
Worker pools sized for steady-state throughput, not peak load.
-
Autoscaling based on sustained backlog, not instantaneous spikes.
-
Clear degradation paths when backlogs grow beyond acceptable bounds.
This architecture shows up in event pipelines, order processing systems, and even user-facing APIs when designed carefully.
What matters is not the specific technology, but the shape of the system. Bursts are absorbed at the edges. Core systems operate within known limits.
Where This Gets Hard in Practice
There are real tradeoffs.
Queues add complexity and operational overhead. Debugging delayed work is harder than debugging synchronous failures. Autoscaling policies require tuning and ongoing attention. Load shedding forces uncomfortable product decisions.
Some workloads cannot be delayed, such as real-time bidding or interactive collaboration. In those cases, the focus shifts to aggressive caching, partitioning, and precomputation.
Finally, bursts are often correlated. Marketing campaigns, breaking news, or external outages can drive traffic and dependency failures at the same time. Designing for these compound events requires chaos testing and uncomfortable drills, not just diagrams.
Common Questions Engineers Ask
How big should my buffer be?
Big enough to absorb the largest burst you are willing to tolerate, small enough that backlog drain time stays acceptable. This is a product decision as much as a technical one.
Is serverless the answer to burst traffic?
Sometimes. It shines for spiky, stateless workloads. It struggles with cold starts, stateful dependencies, and unpredictable cost profiles under sustained load.
Can caching replace all of this?
No. Caching reduces load, but cache misses during bursts can be catastrophic. You still need backpressure and isolation.
The Honest Takeaway
Designing for burst traffic without overprovisioning is less about capacity and more about discipline. You accept that not all work is equal, not all traffic deserves the same treatment, and not all failures are bad.
The teams that handle bursts well are not the ones with the biggest clusters. They are the ones who know their limits, enforce them early, and build systems that bend instead of breaking. That work is slower and more nuanced than throwing hardware at the problem, but it pays off every time the graph goes vertical.
A seasoned technology executive with a proven record of developing and executing innovative strategies to scale high-growth SaaS platforms and enterprise solutions. As a hands-on CTO and systems architect, he combines technical excellence with visionary leadership to drive organizational success.