As hackers begin to exploit vulnerabilities deeper in the technology stacks around us, we need to focus on security along multiple vectors. An effective security strategy will address the entire end-to-end application with a defense-in-depth posture that minimizes vulnerabilities at every level of the stack. Incorporating these best practices into the automation and infrastructure processes around DevOps scenarios will provide the best overall outcome.
Recent high-profile security breaches have led to a litany of stories about personal information and financial data being stolen or exposed by hackers. Early publicity often focuses on the human aspect???whose credentials were compromised, what sort of data was collected and how to check whether you were affected. A second wave of articles then focus on the hacker’s methodology, such as brute force, phishing an administrative credential, targeted malware and more. Finally, we get a full post-mortem, following the trail from network entry to infected target to data collection. And that’s where the fun begins.
The Shift to IoT
Over time, the details and targets of these attacks have evolved, to focus less on human interaction and more on technical vulnerability. Convincing a single user to give up a password or credit card number through a phishing attack or social engineering might be effective, but it doesn’t scale. Instead, hackers have realized that scenarios targeting vulnerabilities lower on the tech stack can quickly scale to collect data from thousands or millions of victims; collecting a database of passwords is a lot more efficient than collecting one at a time.
As threats progress down the stack, they start to attack APIs that have been opened without sufficient security and management capabilities. For Snapchat, Moonpig and the IRS, even some basic intelligence about transaction rates could have made a huge difference in the number of victims; more sophisticated API Management solutions could have prevented it entirely. However, hackers aren’t stopping at the API layer. The surge in IoT use cases has brought along new threats at every level, from forcing Point of Sale machines to record customer information as they process transactions, to manipulating the baseband chip that communicates with the mobile network in modern smartphones, to taking over a connected car via its in-dash infotainment system.
In an increasingly connected world, our Things need to be able to talk to one another, and to the rest of the Internet. Checking out at a department store may reach out to 10 different systems for item details, inventory, mobile device-to-POS transaction processing, backend credit card processing, customer relationship management, social integration, and many more. Our cars can get news stories and weather forecasts and streaming music and driving directions and restaurant reservations. Connected medical devices can make changes to body chemistry or heart rhythms based on feedback from other sensors. These IoT scenarios make our lives easier and richer, but the result of vulnerabilities in the connected systems can be catastrophic. For example, the platform looking up movie show times while driving to the theater is often the same system that can lock/unlock the car doors or perform a remote start/stop, as Jeep recently discovered when an insecure entertainment system provided hackers with a way to remotely shut down a vehicle.
Defense in Depth
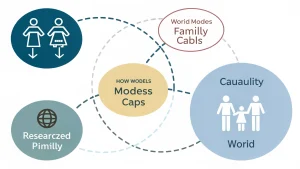
The sheer magnitude of potential threat vectors in an Internet of Things scenario demands “defense in depth.” This concept is a common one in military and security circles, but is less often applied when dealing with everyday applications. It suggests that security should be taken into consideration at each layer of the technology stack???the layers most commonly included are data, application, host, internal network, perimeter, physical and policies, procedures and awareness. Each of these layers has a set of possible threats and remediation for those threats. A network firewall or security gateway can provide a secure perimeter; SSL can provide transport-layer data security; locked gates and biometric access scanners might provide physical protection to a server in a data center; and tricking someone out of their password using social engineering can be prevented through some simple awareness and standard operating procedures.
A combination of configured security and strict security policies should work together to protect everything, from human interactions to data encryption. If something is missed at one layer, it should be picked up at another layer by risk evaluation or log analysis or any of a number of tools designed to provide operational visibility, threat detection and breach remediation. Defense in depth provides the best overall chance at secure application delivery.
End to End
Beyond looking at every layer of the stack, a truly rigorous security posture must be able to follow a transaction from end to end across every device or system that may have access to critical components, and ensure this same layered defense in depth across each one. With the number of systems involved (phones, cars, peripherals, servers) and the layers to be protected, the complexity of the problem increases. With the expanding IoT market, these issues need to be addressed up front; while nothing can stop the continued adoption of IoT, failure to look at the bigger picture will result in more negative headlines.
Focus on User Experience
If we recognize the importance of security across all of these IoT (and non-IoT) scenarios, how can we build applications that still delight our customers? For client-side developers, the Holy Grail is a fantastic user experience. The last thing they want to worry about is implementation of multiple layers of security across the network, application and data layers. That’s why developers should take advantage of IT-managed security infrastructure to enable rapid development without major impediments, so they can deliver apps to market more quickly. Backend IT architects should similarly be able to focus more on the data and logic being delivered than the security implementation, and make use of configuration-driven security infrastructure.
DevOpsSec
Taking this one step further, security should be deployed as part of the larger application development process. For enterprises using DevOps methodologies, this means bringing security to the table early in the process and turning it into “DevSecOps.” It means rolling code testing and vulnerability scans into the deployment process. It means automating the provisioning of security infrastructure right alongside (or in front of) the application architecture. The result is the best possible outcome from a true end-to-end and defense-in-depth strategy.
About the Author
Jaime Ryan?is Senior Director, Product Management & Strategy at CA Technologies, leading integrations between CA API Management and other CA and partner technologies. Jaime was at Layer 7 prior to CA’s acquisition in June 2013, where his responsibilities included technical strategy, partnerships, evangelism, marketing and analyst relations. He has been building secure integration architectures as a developer, architect, consultant and author for the last fifteen years, and currently resides in San Diego with his wife and two daughters.
Charlie has over a decade of experience in website administration and technology management. As the site admin, he oversees all technical aspects of running a high-traffic online platform, ensuring optimal performance, security, and user experience.