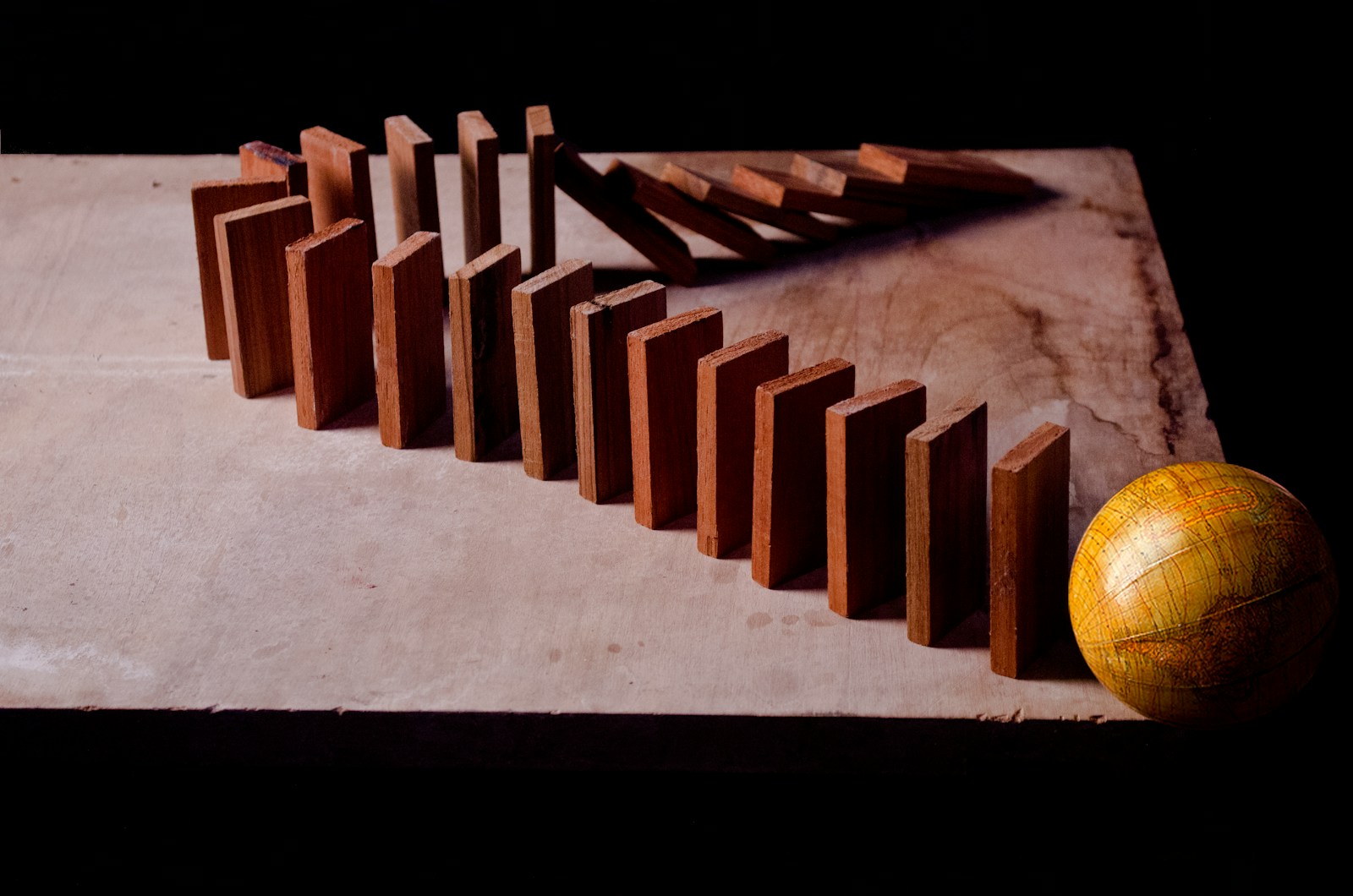
You know the feeling: the service looks clean in code review, latency p50 is fine, and the dashboards are mostly green. Then one dependency starts timing out, queues back up, retries explode, and suddenly your “simple” microservice is the blast radius. The resilient systems are not the ones with the most tooling. They are the ones whose authors assumed the network lies, downstreams fail, deploys go sideways, and humans debug at 3 a.m. The difference is rarely a single big design choice. It is a set of subtle patterns baked into boundaries, defaults, and failure semantics that either keep entropy contained or let it cascade.
1. They make failure a first-class API behavior
Brittle services treat errors as exceptional. Resilient services treat them as a normal output shape. That shows up in contracts: timeouts are defined per call, error codes map to actionable categories, and you can tell “retryable” from “not retryable” without reading logs. When you ship a client library or publish an internal API, your biggest reliability decision is often your error taxonomy. If you collapse everything into 500, the caller can only guess. Guessing turns into retries. Retries turn into thundering herds. A small but powerful move is to standardize on a limited set of error classes and make them observable. In one payments stack I’ve seen, the difference between “dependency_timeout” and “validation_rejected” prevented an auto-retry policy from amplifying a downstream brownout into a full outage.
2. They default to bounded work, not “best effort.”
Brittle services accept unbounded inputs, unbounded fanout, and unbounded concurrency, then hope autoscaling saves them. Resilient services assume load will exceed capacity and design the “no” path. That can be as simple as a hard cap on in-flight requests, or as structural as per-tenant queues and budgets. When you add a feature that multiplies work, like N calls per request, resiliency lives in the default. Do you cap N? Do you degrade? Do you reject early? The most reliable services I’ve worked on have a clear philosophy: shed load close to the edge, and do it predictably. Envoy/Linkerd-style circuit breaking and rate limiting help, but the pattern is deeper than a proxy. It is a worldview: every resource is finite, so every codepath needs a bound.
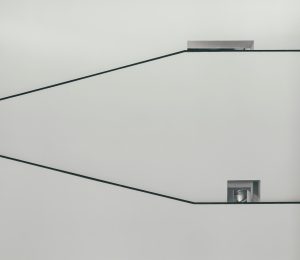
3. They use timeouts like a design language
Timeouts are not a knob you tune after the incident. They are part of your service architecture. Brittle systems pick a single number and sprinkle it everywhere. Resilient systems compose time budgets across calls and propagate deadlines. If the upstream gives you 800 ms, you do not spend 790 ms waiting on a dependency and then attempt three more operations. Deadline propagation forces honesty. It also makes failure faster, which sounds counterintuitive until you watch a slow dependency drag an entire fleet into thread starvation.
A useful mental model: every hop spends from a shared budget, and every hop must reserve time for cleanup and a meaningful response. If you cannot, fail fast with a specific error. One of the most effective “subtle” changes I’ve seen was moving from ad hoc timeouts to a single deadline header enforced consistently. Tail latency dropped, but more importantly, incidents stopped cascading across tiers.
4. They treat retries as a distributed systems hazard
Retries are often sold as reliability. In production, retries are load multipliers. Brittle services retry by default, at the same cadence, and at the same layer. Resilient services decide where retries are allowed, how many, and under what signals. They use exponential backoff with jitter, and they stop retrying when the system is telling them it is unhealthy.
The subtle design pattern is to make retries explicit and budgeted. A single request should have a maximum retry “cost,” and that cost should be visible in metrics. Otherwise, you get the classic feedback loop: dependency slows, callers retry, dependency slows more. Netflix Hystrix-style bulkheads and circuit breakers made this failure mode legible to a generation of teams, but you can implement the same principles without that specific library. The key is to design retries as a policy with guardrails, not a reflex.
5. They separate “control plane correctness” from “data plane correctness.”
Brittle services overload their hot path with everything: config fetches, feature flag evaluation, auth token introspection, and dynamic routing, all done synchronously. When the control plane hiccups, the data plane goes down too. Resilient services treat the control plane as eventually consistent. They cache configs, tolerate stale flags, and keep serving with the last known good state. That is not just performance. It is resilience to the inevitable outage of your own internal platform.
A tiny example: if a feature flag service times out, do you fail the request or fall back to a default? The resilient answer usually depends on the risk profile, but it is always intentional. You can even encode it: flags that gate safety fail closed, flags that gate experimentation fail open. Making that distinction explicit prevents a “flags outage” from becoming an “everything outage.”
6. They make idempotency cheap and common
Idempotency is a reliability primitive disguised as an application concern. Brittle services assume “exactly once” because it is conceptually neat. Resilient services assume “at least once” because it is reality. If you cannot safely repeat an operation, every retry is dangerous, every partial failure is a data integrity risk, and every incident response turns into a forensics exercise.
Patterns that show up in resilient systems: idempotency keys on write APIs, deterministic request identifiers, and storage models that can reconcile duplicates. Stripe’s idempotency key approach for payments APIs is famous for a reason: it acknowledges that clients will retry under ambiguous conditions and makes that safe. Even internally, treating idempotency as default reduces fear around timeouts and client behavior, which means you can be aggressive about failing fast without causing double-writes.
7. They decouple with queues, but they also bound the queue
Queues can turn spikes into steady work, but they can also turn failures into deferred catastrophes. Brittle services enqueue everything, then discover later that the backlog is days long, the retry topic is melting, and consumers are silently failing. Resilient services design queue semantics: max backlog, dead letter behavior, replay strategy, and per-message time-to-live. They know what happens when the queue is full, not just when it is empty.
The subtle pattern is treating backlog as a signal, not a buffer. If your system can “accept” work it cannot complete within the business SLO, you are lying to the caller and to yourself. Mature teams choose one: reject now, or accept with a concrete expectation and a way to communicate progress. Everything else is operational debt that comes due during the worst possible week.
8. They build bulkheads around the things that fail together
The most brittle outages are the ones where unrelated workloads share a dependency: a thread pool, a DB connection pool, a cache cluster, a node, a Kubernetes namespace. Resilient services isolate failure domains intentionally. That can be per-tenant partitions, separate pools per dependency, or even separate deployments for “heavy” and “light” request types. Bulkheads look like extra complexity until the first time one noisy neighbor would have taken down your entire API.
This is also where platform choices matter. On Kubernetes, if all your request types share the same pod resources and autoscaling signals, you can end up scaling for the wrong thing. Resilient services use differentiated queues, priorities, and resource classes. They keep the critical path protected even when the system is under stress.
9. They make partial degradation a product decision, not an incident hack
Brittle services either work or they do not. Resilient services have planned degradation modes: cached reads, reduced personalization, skipping non-essential enrichments, or serving last known results. The key is that these modes are not improvised during an outage. They are tested, exercised, and owned.
A reliable pattern is to explicitly label optional dependencies. If an enrichment call fails, you return the core response and annotate that enrichment is missing. If your system cannot tolerate missing data, that dependency is not optional, and you should treat it as such in SLOs and capacity planning. The subtle part is social: product and engineering agree ahead of time what “good enough under stress” looks like, so you are not negotiating in the middle of a paging storm.
10. They debug with high signal, low ceremony observability
Resilient services do not just emit more telemetry. They emit the right telemetry. In practice, that means consistent trace boundaries, stable cardinality, and logs that answer “what happened” without a forensic expedition. Google SRE’s emphasis on golden signals is useful here because it forces prioritization: latency, traffic, errors, and saturation. If you cannot see those per dependency and per critical endpoint, you are blind during degradation.
The subtle design pattern is designed for debuggability in the request lifecycle. Correlation IDs are propagated everywhere. Errors include enough context to classify the failure without dumping secrets. Metrics have labels that match your mental model of the system, not your org chart. And your dashboards distinguish symptoms from causes, so your on-call does not chase noise. This is not observability as art. It is observability as an operational interface.
Final thoughts
Resilience is rarely one feature you bolt on. It is a collection of defaults and boundaries that assume failure, limit blast radius, and preserve debuggability under stress. The brittle services are the ones that hide failure semantics, outsource limits to autoscaling, and treat retries as magic. The resilient ones decide upfront how they fail, how they shed load, and how they stay understandable when reality stops being polite. If you want a practical next step, audit your timeouts, retry budgets, and idempotency story. Those three alone reveal whether your service is designed to survive the messy world in which it actually runs.
A seasoned technology executive with a proven record of developing and executing innovative strategies to scale high-growth SaaS platforms and enterprise solutions. As a hands-on CTO and systems architect, he combines technical excellence with visionary leadership to drive organizational success.