The Domain Name System, shortened to DNS, is a key part of translating readable domain names into IP addresses. In the past decade, the need for DNS security has increased as it has become a target for cybercriminals looking to exploit vulnerabilities.
It’s worth reminding ourselves of what a DNS exploit can result in. The primary concern is a data breach, where sensitive information, such as login credentials or, worse, financial data, is intercepted. If not a full redirect to a malicious site, you’re looking at general network outages and the reputational damages – or loss of sales – that come with that.
Understanding DNS vulnerabilities
DNS is susceptible to attacks in part because of its cache-poisoning vulnerability. This vulnerability allows false information to be inserted into the DNS resolver’s cache, meaning it returns incorrect IP addresses. The danger here is that users are redirected to malicious websites, and it’s quite difficult to detect.
DNS tunneling is another concern, in which attackers bypass network firewalls and exfiltrate data, encoding it within DNS queries and responses. The most well-known attack, however, has been the DDos attacks, which stand for Distributed Denial of Service. These highly targeted attacks overwhelm DNS servers with a flood of traffic, making them incapable of responding to legitimate requests.
DDos attacks became widely known in the eSports and Twitch community, in which streamers were targeted live on air. So, what can we do to stay safe from DNS vulnerabilities?
DNS Security Best Practices
The first step is deciding on your web hosting provider. HostingCanada.org reviews the security of many top hosters, though you may have already decided. Fortunately, many of the DNS security strategies can be implemented on top of any top provider. The site also provides insights into different hosting options, helping users make informed decisions about performance, reliability, and cost-effectiveness.
Organizations need a multi-layered approach to DNS security. The first best practice is the deployment of DNSSEC. Domain Name System Security Extensions uses digital signatures to ensure the authenticity of DNS data. In other words, by implementing DNSSEC, you can protect against DNS spoofing on your site and cache poisoning attacks, meaning only legitimate users are directed.
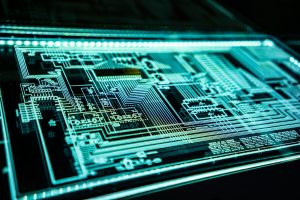
DNS Firewalls
DNS firewalls are also necessary to keep your website safe. These analyze DNS traffic and ultimately filter through it, blocking access to known malicious domains. These firewalls can be integrated with threat intelligence feeds to ensure they’re updated with the latest red flags. Of course, regularly updating the DNS software will help patch any known vulnerabilities.
DNS logs can also be useful data to analyze. These can help point out potential security incidents, and the more logs you have, the better your pattern recognition can become. However, a spike in DNS traffic alone can be suspicious, along with unexpected query patterns. The end goal is to identify the threats before they become security breaches.
Another consideration is to implement access controls. Here, you can restrict access to DNS management interfaces through various authentication mechanisms and a properly segmented DNS infrastructure from other network components – this is particularly important when hiring others to work on your website with you.
Tools and Incident Response
It’s worth looking at advanced monitoring tools that can provide better real-time insights due to their richer pattern recognition training data. Outsourcing this, to a degree, can not only reduce false positives and better identify novel, new attacks, but it can alleviate your own resources spent on threat detection. Real-time alerts can be set, where you’re notified of any anomalies.
Penetration testing shouldn’t be ignored here, either. By having a professional team intentionally attack your website, you can see how it responds. They may use DNS enumeration or fuzzing to identify weaknesses and consult on how to fix these. While pen testing just for DNS isn’t all that common, it could be a part of a broader service to check our site’s defenses.
A well-defined response plan will be central to handling DNS incidents. The plan will outline the procedures that need to be taken when containing compromised systems and collaborate with DNS registrars to mitigate the impact.
After the event, it’s important to conduct an analysis to identify the root cause and extent of the damage. Ultimately, you need to learn from every incident; otherwise, it may happen again in precisely the same way.
Final Word
DNS security is profoundly overlooked, considering how vulnerable it can leave sites to not just downtime but potentially dangerous redirects. DNS infrastructure needs to be within the scope of your broader cybersecurity approach, and this goes for any penetration testing. By combining the best practices with DNSSEC deployment, you should be able to build above-average resilience.
Rashan is a seasoned technology journalist and visionary leader serving as the Editor-in-Chief of DevX.com, a leading online publication focused on software development, programming languages, and emerging technologies. With his deep expertise in the tech industry and her passion for empowering developers, Rashan has transformed DevX.com into a vibrant hub of knowledge and innovation. Reach out to Rashan at [email protected]