A brief announcement has sparked debate across the software world. A company introduced the first three “frontier agents” designed to change how teams build, secure, and operate software. The statement hints at a new push to automate work now done by developers, security teams, and site reliability engineers. It raises hopes for faster delivery and safer systems, along with questions about control, risk, and proof.
“The first three frontier agents revolutionize how you build, secure, and operate software.”
The claim suggests a new wave of AI-driven helpers. These agents appear aimed at the core steps of modern DevSecOps. The idea is to bring AI into coding, testing, threat detection, and on-call response. The approach could appeal to teams pressed by talent shortages and rising complexity.
What These Agents Likely Do
While details remain limited, the three-agent framing maps neatly to common workflows. One agent would focus on building software. A second would watch for vulnerabilities. A third would help run services in production. Each would need tight access controls and clear audit trails to gain trust.
- Build agent: code suggestions, test generation, and release checks.
- Security agent: dependency scanning, policy enforcement, and risk alerts.
- Operations agent: incident detection, runbook action, and postmortem summaries.
The company’s statement sets a high bar. Success will depend on how these agents plug into existing tools like source control, CI pipelines, ticketing, and observability platforms. It will also depend on how well they explain their actions.
Context: AI Moves Into DevSecOps
AI-assisted coding tools are now common in many teams. Security platforms use machine learning to spot anomalies and triage alerts. Operations teams rely on automation for scaling and failover. The next step is autonomous agents that act across systems with minimal input.
Past attempts to automate release gates and incident fixes show mixed results. Gains often come with trade-offs in false positives, model drift, and maintenance. Teams want faster work, but not at the cost of outages or missed threats. That tension shapes the reaction to this announcement.
Promises and Proof
If the agents work as promoted, developers could spend less time on routine tasks. Security teams could reduce manual reviews. On-call engineers could cut time to recover. Yet buyers will look for evidence before changing workflows.
Key questions for early users include:
- Accuracy: How often do the agents produce correct code changes or alerts?
- Governance: Can teams set policies, approvals, and rollbacks?
- Privacy: How is source code and production data protected?
- Cost: Do savings offset compute and integration expenses?
- Interoperability: Do the agents support open standards and vendor-neutral logs?
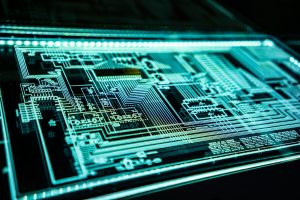
Security First or Security Later?
Security leaders often ask whether AI creates new attack paths. An agent with write access to code or infrastructure is a rich target. That means strong identity, least-privilege design, signed actions, and tamper-proof logs. It also means clear “break glass” procedures when an agent misbehaves or faces an ambiguous task.
Red-team exercises can help. So can staged rollouts that start in non-production. Many organizations will test these agents in shadow mode before granting write access.
Operations: From Advice to Action
In operations, the line between recommendation and action matters. An agent that pages humans with precise context already adds value. One that executes playbooks must meet higher standards. Teams will look for guardrails such as change windows, circuit breakers, and canary releases. They will also ask for simple ways to replay incidents and review each step the agent took.
Industry Reaction and What to Watch
Analysts and engineers say interest in AI agents is high, but adoption will hinge on transparency. Clear reporting and human-in-the-loop options often decide success. Reference customers, reproducible benchmarks, and public postmortems could build trust.
Areas to monitor in the coming months include:
- Real-world case studies in regulated sectors.
- Support for popular stacks, from Kubernetes to serverless.
- Pricing models that match usage rather than flat seats.
- Independent security reviews and SOC 2 or ISO attestations.
- Tools for prompt management, versioning, and safe rollbacks.
The announcement sets an ambitious goal. It points to a future where AI assists at every stage of the software lifecycle. The next step is proof in production. Teams will look for small wins: safer code merges, quieter alert queues, and faster incident recovery. If these agents deliver measurable gains without new risk, they could change daily work for developers, security analysts, and operators. For now, the focus shifts to pilots, metrics, and transparency.
Rashan is a seasoned technology journalist and visionary leader serving as the Editor-in-Chief of DevX.com, a leading online publication focused on software development, programming languages, and emerging technologies. With his deep expertise in the tech industry and her passion for empowering developers, Rashan has transformed DevX.com into a vibrant hub of knowledge and innovation. Reach out to Rashan at [email protected]