
Free Microsoft 365 Security Training
On October 11, 2023, the need for comprehensive and effective cybersecurity in a modern business environment was highlighted as Microsoft 365, a cloud-based platform for productivity, brought together tools like

On October 11, 2023, the need for comprehensive and effective cybersecurity in a modern business environment was highlighted as Microsoft 365, a cloud-based platform for productivity, brought together tools like

In today’s technologically advanced world, the traditional doorbell has evolved into a state-of-the-art device that integrates multiple functions and enhances security. Video doorbells, with their built-in cameras, microphones, and Wi-Fi

In today’s increasingly digital landscape, businesses of all sizes must prioritize cyber security measures to defend against potential dangers. Cyber security professionals suggest five simple technological strategies to help companies

The banking, financial, and insurance (BFSI) sectors are pioneers in digital transformation, using web applications and application programming interfaces (APIs) to provide seamless services to customers around the world. Rising
Are you wondering how much it costs to build a website? The approximated cost is based on several factors, including which add-ons and platforms you choose. For example, a self-hosted

Today, many businesses are adopting cloud computing services. As a result, it’s important to recognize that security measures for data in the cloud are different from those in traditional on-premises
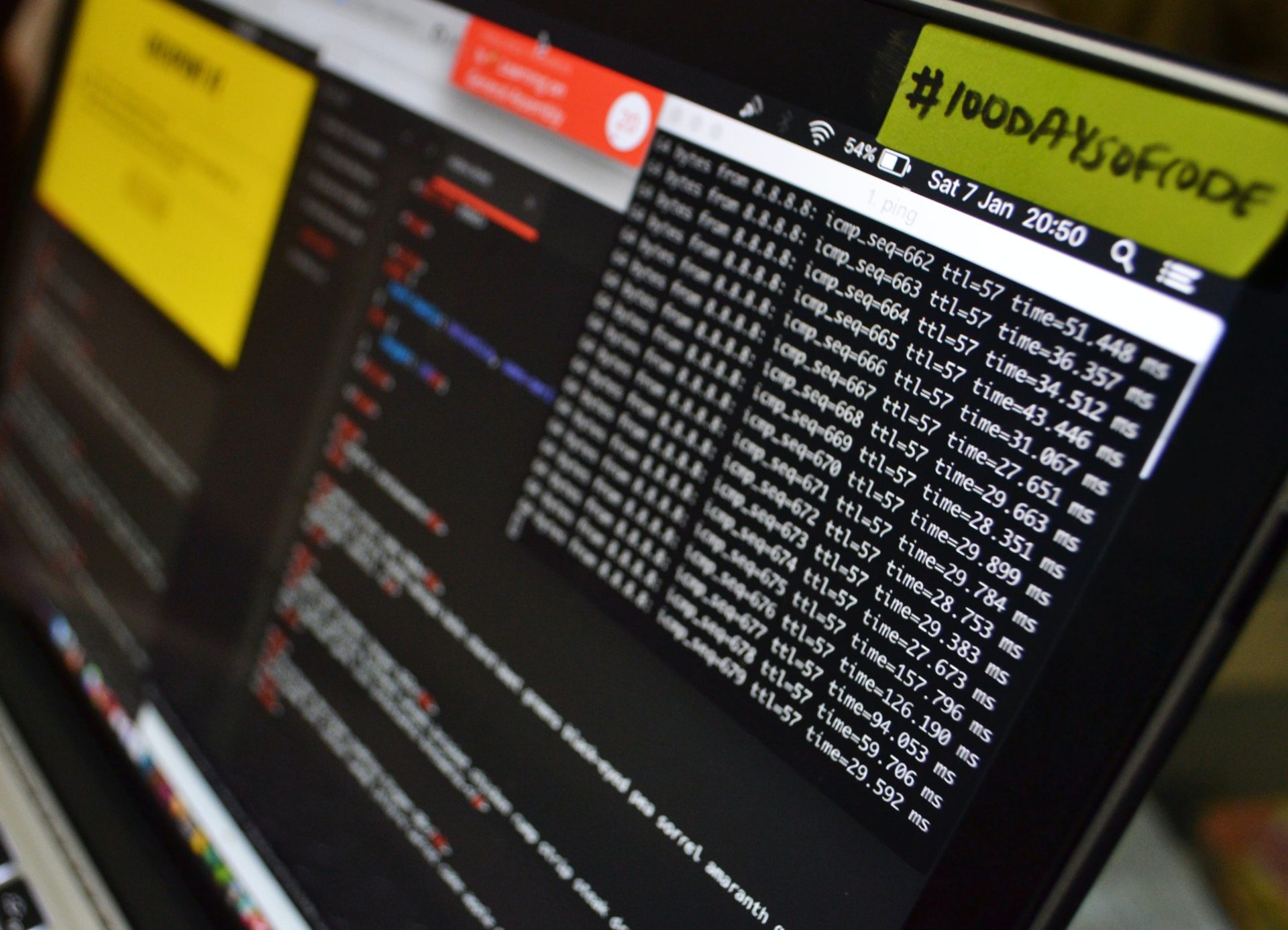
A major security breach recently occurred at a well-known company, leading to unauthorized access to sensitive customer data. Sources within the organization have confirmed that the technology team is diligently

The Web Security Academy has recently introduced new educational courses designed to offer a comprehensible and straightforward journey through the intricate realm of web security. These carefully designed learning courses

Recently, Cloudflare introduced its One Data Protection Suite, an extensive collection of sophisticated security tools designed to protect data in various environments, including web, private, and SaaS applications. The suite