Since 1998, DevX has helped people start businesses, build websites, and provide enterprise technology to people globally. Interviewing the likes of Microsoft’s co-founder, Steve Ballmer, the publication brings comprehensive, reliable, and accessible insights to the Internet.






Using a loop and the mathematical formula for a spiral, you can use pset(x,y) to plot the points returned by the formulas. The variables a and b determine the shape

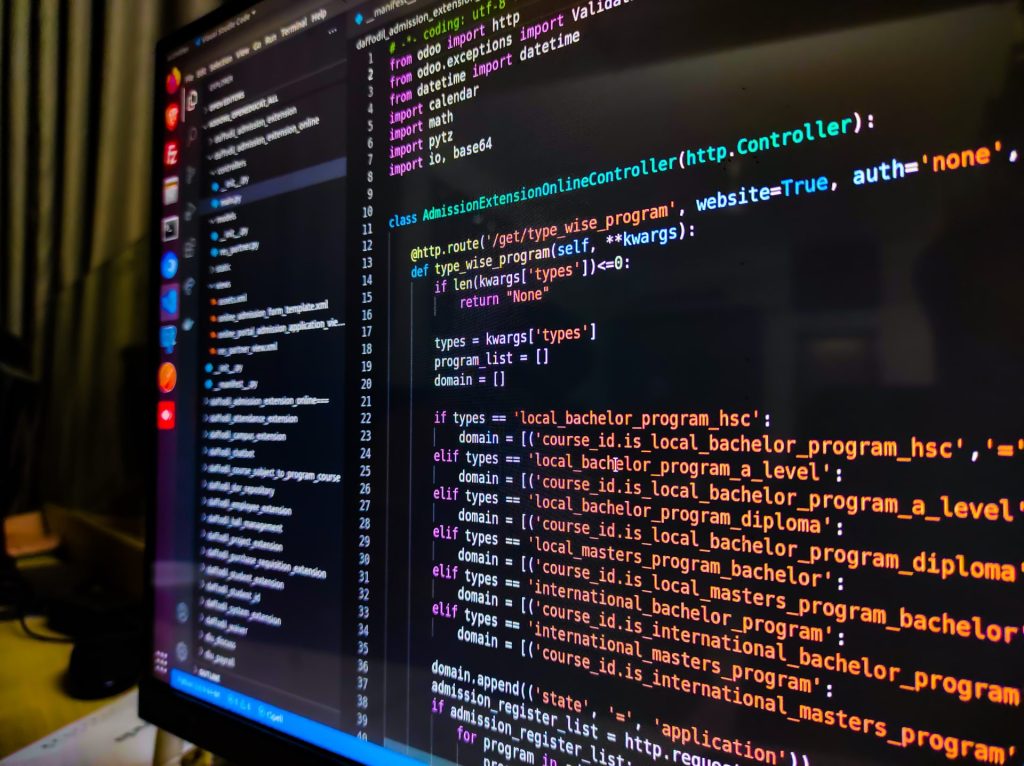
ualcomm Brew’s component-oriented architecture and rich collection of components?interfaces, in Brew parlance?makes it easy to find a component to accomplish a particular task, such as decompressing an incoming stream (try

rawing text in Visual Basic 6 was all very simple?both the process and the results. First, you would set a form or PictureBox’s CurrentX and CurrentY properties and then call

This tip shows you how to display the entries from a JAR/ZIP archive using the java.net.URL class. The key in this example is the URL construction. import java.net.*;import java.io.*;import java.awt.*;import

The ability of Windows XP to save passwords for Web sites and network resources can be very convenient. Of course, it’s true that anyone with access to your computer can

Suppose you want to have a primitive type with a null (or an unknown) value. This is where you would use a nullable type. Nullable types have the following characteristics:

This function clears all occurences of extra white space (spaces, tabs, blank lines) and programming comments beginning with ‘;’ in a file and saves the cleaned file as another file.

he brand new 3.0 version of Windows Sharepoint Services (WSS) is no lightweight release. In fact, if you’ve had a chance to look through the new WSS SDK it’s not

icrosoft’s Visual Studio Team System (VSTS) focuses on the issue of dealing with complex software projects built by a large team. VSTS has all the ingredients needed for a distributed

Radio Frequency Identification (RFID) system is an identification system that uses radio waves to retrieve data from a device called a tag or transponder. RFID surrounds us in our daily

transaction is a very common operation in our daily lives as well as in the computing world. For example, when you try to deposit a check issued by your boss,

fforts to simplify application globalization and localization have definitely succeeded over the past few years. ASP.NET 2.0 made the process of localizing resources and deploying them with applications easier for

hy, oh why, should you use yet another file to house string, image, and binary resources? With Brew there are several good reasons. As every experienced developer knows, each handset

he .NET framework provides strong support for accessing Active Directory Services, letting you create, edit, delete, and search for directory objects efficiently. This article discusses the benefits of Active Directory

This recursive function finds a control on a form by its name. //written in C#/// <summary>///Recursive function to find control on the form by its name/// private Control _co;private Control

If you have images that are supposed to have transparent portions, but have lost the transparency information, you can use Microsoft Word to restore the transparent color. First, paste the

The easiest way to constrain an HTML input box to uppercase is to use the STYLE attribute inside the INPUT tag. Suppose you have the following code: <input type=”text” name=”big”

he long-awaited Java SE 6 is upon us. This latest version of the Java SE environment brings a number of new features and enhancements, such as integrated support for scripting

This tip shows you how to create XMLSchema datatypes direct from Java, using the javax.xml.datatype.* package. In this example you’ll create a Duration object (xs:duration in XMLSchema) and a XMLGregorianCalendar

he Web has undergone some major changes during past few years. What started purely as static HTML pages now includes dynamic pages with personalization, improved performance, and new technologies such

essage Queuing (MQ) has long been a foundation for applications that require asynchronous and disconnected communications. Implementations of Message Queuing such as Microsoft’s MSMQ, IBM’s WebSphere MQ, TIBCO’s Rendezvous, and

f you have ever received a package from one of the main courier companies (such as UPS, DHL, or FedEx), you have no doubt been asked to sign for the

mployees and clients can make better decisions, increase productivity, and realize other benefits when they can access company information (statistics, presentations, reports, etc.) accurately and in a timely fashion. Because

any topics flit through my mind; I thought I’d share a few…. 1) Many developers use Web services. WCF is coming, but those pronouncing .NET remoting as dead should talk

eb applications today do a number of things. A Web site could be a banking site, a content management system, or a news center. In spite of this diversity, it

am the host of “.NET Rocks!”, an Internet audio talk show for .NET developers online at www.dotnetrocks.com and msdn.microsoft.com/dotnetrocks. My co-host Richard Campbell and I interview the movers and shakers

have a friend with whom I have a never-ending IM conversation. You know what I mean: We never say “Hello” or “TTYL”. Conversations just gradually flow in and out, as

ast month I was corresponding with a CoDe Magazine reader. I’ve had similar conversations numerous times, only this conversation ended with a twist. The author asked: I didn’t receive the

ultithreaded applications are notoriously difficult to write, test, and debug. However, to take full advantage of the added performance potential of multicore desktop and laptop systems, developers now face the

he first installment of this three-part article series introduced the core concepts of ADO.NET vNext, including the Entity Data Model (EDM), Entity SQL, and the Mapping Provider. It also discussed