APIs are the unsung heroes of modern software. They quietly ferry sensitive data between services, users, and third parties. But they’re also prime targets for attackers, and most teams don’t give them the defensive attention they deserve. If you think static analysis or a few pentest tickets can substitute for true threat modeling, you’re already behind. And if you’re not modeling threats early and often, your API isn’t just unprotected—it’s a map to your most valuable systems.
I’ve watched teams scramble after a data leak, only to find out it started with an overlooked API endpoint exposed to the public internet. The truth? You don’t need to be a security expert to prevent this. You simply need a lightweight, consistent threat modeling process that integrates seamlessly into your build cycle.
Why APIs Are a Magnet for Attackers
Before launching their probes, attackers often study a comprehensive web API security landscape overview, which is why it’s crucial to understand that terrain from the outset.
Attackers love APIs because they’re deterministic and richly documented—a goldmine compared to UI fuzzing or human-dependent phishing. An exposed API is like an open invitation to explore what your system can do without requiring a UI tour. And once attackers find one vulnerable route, they’ll start chaining it with other calls or probing permission misconfigurations.
Most organizations maintain multiple APIs for different audiences, including the public, partners, and internal users. Each has its own risks. Public APIs are often rate-limited but over-permissive. Partner APIs are assumed to be trusted and are rarely monitored. Internal APIs? Frequently, the most powerful and least protected.
We’re not just talking about authentication bypasses. Consider the following: excessive data exposure, broken object-level access controls, and insecure defaults in third-party software development kits (SDKs). All of these are on OWASP’s API Top 10 for a reason.
Breaking Threat Modeling Out of the Ivory Tower
Before diving into STRIDE, I always revisit an article on understanding threat modeling foundations and methods to refresh my approach and solidify the exercise in fundamental principles.
Security purists might cringe, but threat modeling doesn’t need to be academic. It doesn’t require a PhD or a multi-day workshop. I’ve helped teams distill it into a 30-minute ritual during sprint planning, and the results are night and day.
The simplest structure that consistently works? STRIDE: Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privilege. For every new or updated API, walk through each of those risks.
After sketching your data flow diagram, you can follow a step-by-step API threat modeling process to systematically identify and rank each potential threat.
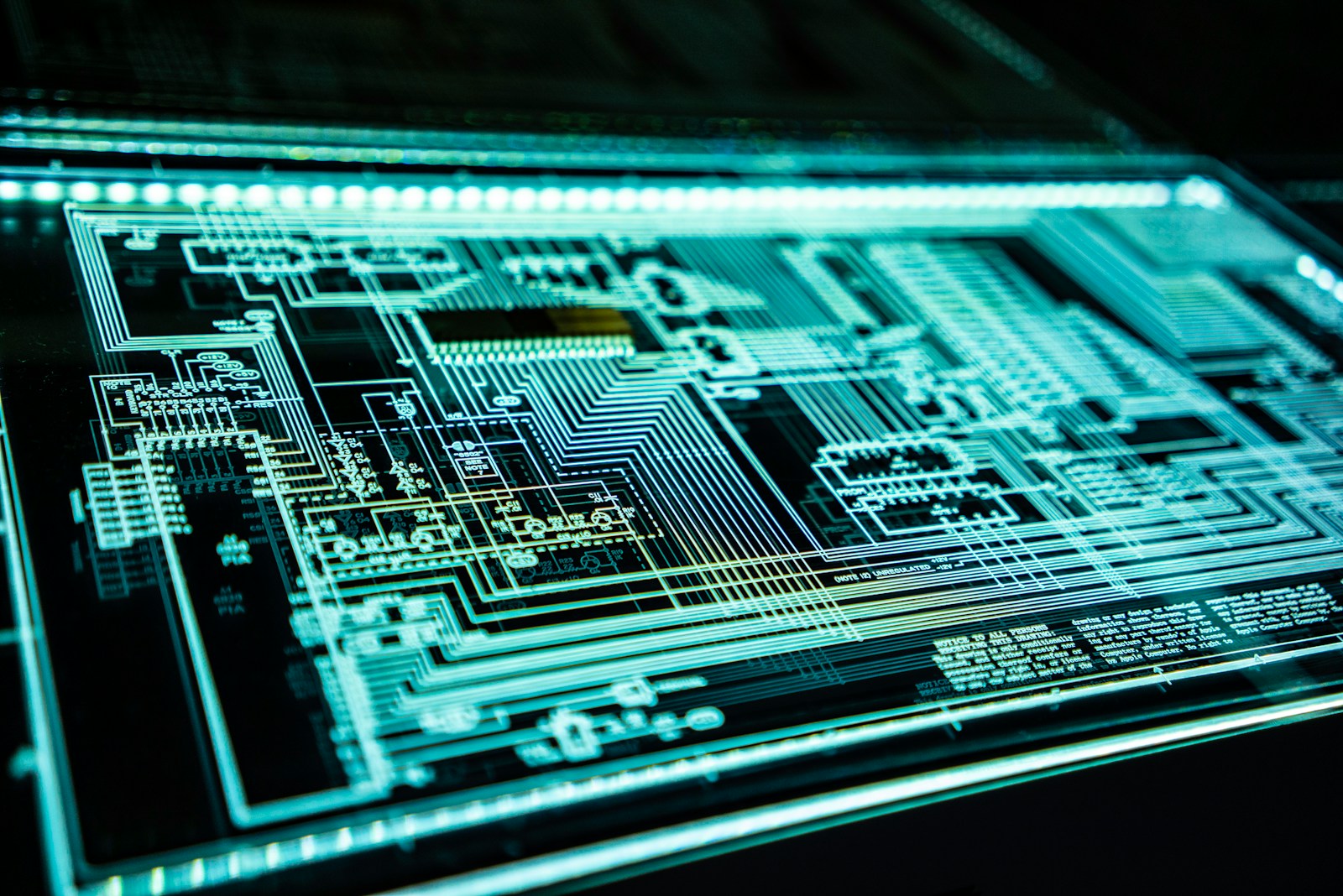
Start with a data flow diagram (DFD). Doesn’t need to be fancy—a whiteboard or even a napkin sketch works. Draw the components: clients, services, auth flows, storage layers. Map out the calls between them. This provides a visual attack surface to identify potential vulnerabilities.
From there, ask questions: Could someone spoof this token? Could this parameter be tampered with? Is sensitive data visible in responses? What happens if this endpoint is flooded? Could a normal user elevate to admin via this route?
Real-World Example: The “Internal” Admin API That Wasn’t
One situation that underscores these risks involved a SaaS startup I worked with. While their setup included what appeared to be a clean API split—/api/public/, /api/partner/, and /api/internal/—things took a turn when one of their reverse proxies was misconfigured during a migration.
Suddenly, /api/internal/metrics was publicly accessible. It returned performance data, including CPU and memory usage, and database query statistics. Not a breach on its own, but recon gold.
While the misconfigured proxy exposed internal metrics, teams practicing layered network security strategies for distributed systems would have had safeguards in place that blocked that exposure before it became an issue.
A bug bounty hunter took it further, chaining the endpoint with an SSRF vulnerability that led to Redis access and, eventually, full control over the background job queue. What began as a seemingly minor exposure turned into a full-system compromise.
Had they walked through STRIDE on that route—even for just five minutes—they’d have flagged the risk of information disclosure and denial of service. A simple access control check or alerting rule could have prevented the entire chain from being compromised.
Making It Stick: Threat Modeling Without Slowing Devs Down
To help teams stay ahead of evolving risks, I recommend pairing your 30-minute threat-modeling ritual with a review of proactive SaaS security best practices for 2025. It reinforces vigilance without slowing your build velocity.
The biggest excuse I hear? “We don’t have time.” Threat modeling may seem like a distraction from the sprint backlog, especially when features are in high demand. However, if you integrate it into your delivery cadence, it becomes one of the most reliable ways to apply best practices for API security across your endpoints consistently.
But here’s the trick: bake it into the rituals you already have.
During sprint planning, flag any tickets that touch API routes.
Set aside 30 minutes per sprint to threat model those tickets—no more.
Assign one dev as the modeler for that sprint. Rotate every cycle.
If you use Jira, create a template that lists the API path, the DFD sketch, and STRIDE flags. This creates a living artifact tied to your backlog and review process.
By integrating cybersecurity best practices into development, you ensure threat modeling artifacts don’t just get discussed—they become part of your actual pipeline.
I’ve seen teams catch insecure default settings, parameter pollution, and even business logic flaws this way, before code is even written. That’s time saved, not wasted.
Tools, Checklists, and Frameworks That Actually Help
You don’t need to roll your own threat modeling process from scratch. Some smart tools and playbooks simplify it.
Lightweight Tools to Start With
- Fuzz testing techniques to uncover API vulnerabilities: Supplement STRIDE and DFDs with runtime edge-case testing.
- OWASP API Security Top 10: Use this as a framing lens. Go down the list with every new endpoint.
- Microsoft’s Threat Modeling Tool: Drag-and-drop DFD builder with STRIDE baked in.
- ThreatSpec or IriusRisk: For teams that want to encode threat models directly into code or workflows.
Simple Documentation Goes a Long Way
Understanding API design essentials for microservice architectures helps you identify and avoid common design-level flaws that can open up vulnerabilities.
Also, don’t underestimate the power of internal wikis. A single shared doc of threat model examples becomes a training tool, a template, and a cultural habit.
I often pair threat-modeling tools with idiomatic library API patterns and best practices to promote security by design.
And when motivation runs low, I keep a running list of real-world API breach stories. These serve as cautionary tales—and a powerful reminder of what’s at stake when modeling is skipped.
Don’t Ship Blind: Know Your Attack Surface
As you map your threat surface, keep in mind that attack vectors evolve. This is especially true when considering the future of API connectivity in IoT ecosystems, where new integrations create new exposures.
APIs are too powerful to treat as just plumbing. Every route you expose is a decision—and an opportunity for attackers. If you’re not visualizing and stress-testing that surface before you ship, you’re asking for trouble.
I’m not saying you need to become a full-time threat modeler. But if you care about uptime, user trust, or your job, you need to know where your API’s soft spots are. Otherwise, attackers will find them for you.
It only takes one missed path to unravel months of solid code. So slow down—just a bit. Map your flows. Think like an attacker. And model accordingly.
That’s how you build fast and ship smart.
Photo by Adi Goldstein; Unsplash
Rashan is a seasoned technology journalist and visionary leader serving as the Editor-in-Chief of DevX.com, a leading online publication focused on software development, programming languages, and emerging technologies. With his deep expertise in the tech industry and her passion for empowering developers, Rashan has transformed DevX.com into a vibrant hub of knowledge and innovation. Reach out to Rashan at [email protected]