Your organization’s devices aren’t just tools—they’re potential entry points, data repositories, and security risks all rolled into one. Whether you’re managing corporate laptops or overseeing a BYOD mobile environment, you face an increasingly complex threat landscape for device data breaches. Each device presents unique security challenges that require specific protection strategies.
The Device Diversity Challenge
As organizations embrace flexible work environments, they face unprecedented challenges in securing data across an expanding ecosystem of devices. Your workforce now operates through a complex web of laptops, tablets, and smartphones, each presenting distinct security vulnerabilities. Implementing comprehensive endpoint protection strategies for these diverse devices has become essential for safeguarding sensitive information throughout your organization.
To protect sensitive data effectively, you need a multi-layered approach combining stringent security policies with thorough user education. This means implementing device-specific protocols while ensuring compliance across all platforms. Your incident response plan must account for various scenarios, from lost devices to network breaches, regardless of the device type involved.
Understanding the Risks
Your devices face multiple attack vectors that can compromise sensitive data, from physical theft and weak authentication to network vulnerabilities and malicious software.
Physical Threats: Lost or Stolen Devices
While cybersecurity often focuses on digital threats, physical loss or theft of devices remains one of the most direct paths to device data breaches. Devices are vulnerable whenever they leave secure premises, whether through accidental loss or targeted theft.
To mitigate these risks, implement thorough physical security measures and device recovery strategies. Start with a detailed risk assessment to identify vulnerable points in your device management system. Launch awareness campaigns so your team understands the importance of physical device security. Deploy theft deterrent technologies like GPS tracking, remote wiping capabilities, and device encryption.
Authentication Vulnerabilities
Despite sophisticated cybersecurity measures, weak passwords remain the most exploitable vulnerability in device-level security. Simple or reused passwords across multiple devices fundamentally leave your digital doors open for attackers. Social engineering attacks can easily compromise these weak credentials.
Implement robust password requirements and thorough credential management systems. Add two-factor authentication across all devices to create an additional security layer. Establish clear password reset procedures that prevent common exploits while maintaining user convenience.
Network Insecurity
Unsecured networks pose a major threat to device data breaches. When connecting to public Wi-Fi networks, sensitive company data becomes exposed to potential interception by cybercriminals.
Without proper protection, attackers can capture data transmissions, including emails, login credentials, and confidential files. Implementing VPN usage provides a secure tunnel for your data on public networks. Develop secure browsing habits, such as avoiding financial transactions on public Wi-Fi and verifying network authenticity.
Software Threats
As organizations rely increasingly on mobile devices and applications, malware and malicious apps have become sophisticated tools for device data breaches. Various malware types target devices, from keyloggers that capture sensitive keystrokes to trojans that create backdoors for data extraction.
Risk exposure extends through seemingly legitimate apps requesting excessive permissions that can secretly access cameras, microphones, or data storage. Phishing attacks now leverage SMS and chat platforms to deliver malicious payloads, while ransomware can encrypt device data and demand payment for recovery.
Regular security updates, careful permission management, and thorough app vetting are essential safeguards against these evolving threats.
Update and Patch Management
When security updates remain uninstalled, devices become increasingly vulnerable to known exploits. Cybercriminals actively target devices running outdated software versions. Without proper patch management, organizations expose themselves to preventable risks.
Legacy system vulnerabilities pose a particular challenge when older devices don’t support the latest security updates. Implement automated update solutions across your device fleet to ensure consistent protection without manual intervention. User awareness training plays a vital role—your team needs to understand the importance of promptly installing updates.
Implementing Device-Level Security Measures
To protect your organization’s data, implement extensive security measures, including strong authentication methods, biometric controls, and full device encryption.
Authentication and Biometrics
Security’s first line of defense starts with robust authentication at the device level. Implementing strong authentication across devices creates multiple barriers against unauthorized access. Combine password management tools with multi-factor authentication to establish layered protection.
Modern biometric security offers enhanced fingerprint and facial recognition protection, reducing reliance on traditional passwords alone. Effective user training ensures your team understands authentication protocols and follows best practices consistently.
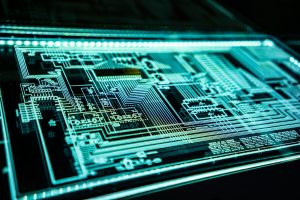
Device Encryption
Full device encryption serves as a critical defense against device data breaches. It protects sensitive data even if devices are lost or stolen, rendering information unreadable to unauthorized users.
The benefits extend beyond basic security—you’ll meet compliance requirements while safeguarding intellectual property and customer information. Modern encryption algorithms provide robust protection without significantly impacting device performance. User education remains critical; your team needs to understand encryption protocols and proper key management.
Mobile Device Management (MDM)
Implementing a robust MDM solution is crucial for effectively managing growing fleets of mobile devices. MDM provides centralized control over device compliance policies and user access, ensuring data security without sacrificing productivity.
Through MDM, you gain powerful remote management that lets you enforce security standards, monitor device status, and implement data loss prevention across all connected devices. You can deploy security updates, restrict access to sensitive data based on roles, and verify devices meet minimum security requirements before connecting to your network.
Best Practices for Data Handling
To maintain strict data handling protocols, implement the principle of least privilege. This principle limits user access to only what’s necessary for their roles.
Principle of Least Privilege
By restricting data access to only what’s necessary for each user’s role, you significantly reduce your organization’s attack surface and potential vulnerabilities.
Start with a thorough risk assessment of your user base. Analyze job functions and establish precise access control parameters that align with specific responsibilities. Create detailed security policies that clearly define user permissions across different device types and data sensitivity levels.
Secure Data Storage and Sharing
Strong data storage and sharing practices form the foundation of effective device-level security. Implement robust data encryption across all devices while leveraging secure cloud storage solutions that maintain data integrity and accessibility.
To protect sensitive information during transfers, establish secure file transfer protocols and enforce strict access control policies. Deploy end-to-end encryption for both data at rest and in transit. Configure devices to automatically sync with approved secure cloud storage services.
Security Awareness Training
Effective device security starts with a well-trained workforce that understands how to handle sensitive data and recognize threats. Your training program should focus on practical device safety measures, including password management, secure data storage, and safe browsing habits.
Regular threat awareness sessions help your team stay current with evolving cybersecurity risks. Train them to identify phishing attempts, suspicious downloads, and unauthorized access attempts. Establish clear security best practices for company-owned and personal devices used for work.
Adapting to Future Trends
Implement Zero Trust Architecture to stay ahead of evolving security threats. This architecture treats every access request as potentially hostile, regardless of its source. AI-powered threat detection systems can identify and respond to suspicious device activities in real time.
These technologies represent a shift from traditional perimeter-based security to more dynamic, context-aware approaches that better protect your devices and data while maintaining the flexibility your workforce needs in today’s mobile-first environment.
Photo by FlyD; Unsplash
Rashan is a seasoned technology journalist and visionary leader serving as the Editor-in-Chief of DevX.com, a leading online publication focused on software development, programming languages, and emerging technologies. With his deep expertise in the tech industry and her passion for empowering developers, Rashan has transformed DevX.com into a vibrant hub of knowledge and innovation. Reach out to Rashan at [email protected]