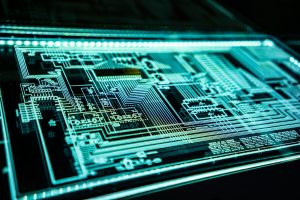
As organizations around the world increasingly rely on cloud infrastructure, the challenge of securing these environments against rapidly evolving cyber threats has grown exponentially. In a compelling look at how artificial intelligence is redefining the future of cybersecurity, Rahul Amte provides valuable insights into the role of AI-powered threat intelligence in predicting and preventing attacks across complex cloud ecosystems. His research explores how machine learning models enhance detection, automate response, and significantly reduce the risks associated with modern cyberattacks.
From Reactive to Proactive: The Shift in Cybersecurity
Cyber Threat Intelligence (CTI) has long been a tool for collecting, processing, and acting on data about potential threats. The integration of AI with CTI is now reshaping this landscape. Using machine learning, AI systems can sift through logs, network traffic, and historical data to identify anomalies, detect zero-day threats, and even predict future attacks.
In one model evaluated in this study, precision and recall scores reached 92.1% and 94.7%, respectively. Most impressively, the model flagged 78% of zero-day threats, outperforming traditional signature-based detection systems. Overall, the risk reduction factor was calculated at 68.3%—a significant improvement over conventional methods.
Why Cloud Needs Smarter Security
Cloud environments are inherently complex, with massive attack surfaces and varied workloads. Legacy security frameworks often struggle to maintain visibility and control, especially as multi-cloud strategies and IoT integration expand. AI, however, excels in this kind of environment.
By continuously learning from data streams and adapting to new threat vectors, AI models reduce false positives and negatives and improve decision-making through real-time insights. These models enhance organizations’ security posture without overwhelming their human operators or requiring constant manual intervention.
Real-Time Intelligence, Real-World Applications
Applications of AI-powered CTI are already taking shape across sectors. In energy grids, for example, AI models trained on cloud data can detect and respond to attacks targeting smart infrastructure. Honeypot systems—deceptive environments designed to lure attackers—are also benefiting from AI, which can analyze patterns from attack attempts and enrich threat intelligence databases.
In industrial IoT and smart manufacturing, AI models based on hidden Markov frameworks have proven capable of identifying anomalies and stopping attacks before they compromise critical systems. From VPN-based evasion techniques to advanced persistent threats, AI is enabling more precise and proactive responses.
Challenges on the Horizon
Despite its promise, implementing AI in cloud security isn’t without hurdles. Privacy concerns loom large, as AI models require extensive data to train effectively. Balancing data protection with analytical power remains a key challenge, especially under evolving regulatory frameworks.
There are also technical threats. Adversarial AI—where attackers manipulate machine learning models—presents new risks. Data poisoning and model inversion can undermine AI defenses, calling for further innovation in explainable AI, adversarial training, and resilience engineering.
Finally, integration is a barrier for many organizations. Existing infrastructure and legacy systems may not easily support AI-driven solutions, requiring investments in both technology and talent. But these are not insurmountable obstacles. Advances in federated learning, where models are trained on decentralized data without compromising privacy, and blockchain-based threat sharing networks are already emerging to close these gaps.
A New Era of Cloud Defense
The results are clear. In head-to-head comparisons, AI-powered systems consistently outperform traditional rule-based and intrusion detection models in detection rate and response time. With a detection accuracy of 93.4% and response time improvements of over 50%, AI systems are reducing the window of exposure and raising the bar for cyber resilience.
In stakeholder surveys, over 85% of security experts expressed strong confidence in AI’s ability to enhance cybersecurity operations—despite lingering concerns around explainability and integration.
This signals a new era for cloud security: one where systems are no longer just defended but intelligently fortified. AI’s ability to predict, prevent, and rapidly respond to cyber threats makes it a foundational tool in the fight against digital threats.
Conclusion
AI-powered threat intelligence is no longer a futuristic concept—it’s becoming the backbone of next-generation cloud security. As attacks become more dynamic and targeted, organizations must move beyond static defenses and adopt adaptive, intelligent systems.
AI is transforming cybersecurity from a reactive process into a predictive, autonomous force by reducing detection and response times, lowering false positives, and providing real-time actionable insights. And while integration, privacy, and adversarial threats remain key concerns, ongoing innovation in machine learning, federated models, and blockchain-based intelligence sharing offers a promising path forward.
In a cloud-connected world where security stakes are higher than ever, AI is proving to be one of our most vital defenses.
Image Credits: Photo by Vladimir Anikeev on Unsplash
Rashan is a seasoned technology journalist and visionary leader serving as the Editor-in-Chief of DevX.com, a leading online publication focused on software development, programming languages, and emerging technologies. With his deep expertise in the tech industry and her passion for empowering developers, Rashan has transformed DevX.com into a vibrant hub of knowledge and innovation. Reach out to Rashan at [email protected]